Letro Protocol & Architecture
A technical overview of how Letro secures the platform with end-to-end cryptography, controlled federation, and deployment options built for regulated communication.
End-to-End Security
Letro protects communication content with sophisticated end-to-end encryption, only the sender and intended recipient(s) are in control. No third parties—including service providers—can intercept or decrypt this information.

How It Works
Device-Side Encryption

Letro encrypts every message or file at the sender’s device before it even leaves the application.
Secure Transmission

Ciphertext, or encrypted data, is transmitted securely over communication channels like the internet or other networks.
Recipient-Only Decryption
Only authorised recipient devices receive the material needed to read the content.
Device Verification

Signed device identities help confirm who sent a message and which device it came from.
Why Security Teams Care
Privacy Guaranteed
E2EE ensures that your sensitive information—ranging from personal data to institutional records—remains confidential.
Tamper Evidence
The encryption process scrambles content in such a way that any tampering with the encrypted message makes it unreadable when decrypted.
This feature makes tampering easy to detect, strengthening the security and integrity of communications. When unauthorized changes occur, they become immediately apparent, reinforcing trust in the reliability of digital communications.
Stronger Compliance Posture
Many data protection laws, including GDPR, mandate data encryption of user-identifiable data as part of their privacy requirements. Encryption and deployment choice help organisations support privacy, security, and residency requirements.
Verifiable Identities
Device verification increases confidence that users are communicating with the right counterpart. Moreover, spam is zero so users can focus on their business without disturbance.
Security Is the Starting Point
Encryption is essential, but communication security also depends on federation and governance. Without these tools, even the most secure tools won’t matter in formal business communication.
Foundation of Security
The Matrix Protocol
Letro is built on Matrix, a well-known open source standard for decentralized real-time communication. Matrix defines open APIs for client-server, server-server, application service, identity, and push interactions. Matrix gives Letro more than encryption. It adds open architecture, federated connectivity, and deployment flexibility that closed messaging stacks cannot offer as naturally.

Key Benefits
Built-In End-to-End Encryption
Matrix supports end-to-end encrypted messaging using Olm and Megolm.
Federation by Design
Separate homeservers can communicate in real time without forcing every organisation into one central system.
Open Standard APIs
Publicly documented APIs make the communication layer inspectable, interoperable, and easier to integrate.
Self-Hosting & Private Cloud
The communication layer can run in infrastructure your organisation controls.
Reduced Vendor Lock-In
Open standards and hosting choice give teams more freedom over deployment and future change.
Secure Group Collaboration
Matrix supports E2E secure room-based communication across multiple users, devices, and organisations. Plus, access control in group conversation.
Sovereign Data Residency and Deployment Control
For enterprise buyers, the real issue is not “trustless” architecture. It is the ability to choose where data resides, who operates the infrastructure, and how separate environments communicate without collapsing into a single vendor-controlled silo.


Data Ownership by the User
Choose Where Data Lives
Choose the geography, operator, and deployment model that match your regulatory, contractual, and operational requirements.
Policy-Aligned Control
Keep operational ownership closer to your organisation instead of defaulting into a shared global tenant. Deploy in the region and environment that fit your governance model.

Data Provenance
Private Servers & Dedicated Infrastructure
A private server changes the trust model by giving your team a clearer operational boundary, monitoring and segmentation for sensitive communication.
Isolated and Air-Gapped Options
For higher-assurance environments, Matrix-based deployments can also run in isolated or air-gapped networks.

Federated Connectivity
Separate Servers, Shared Communication
Different organisations can retain infrastructure independence without losing interoperability.
Authenticated Server-to-Server Trust
Matrix lets separate organisations keep separate servers while still communicating across approved environments. Private servers authenticate each other and exchange data through signed federation APIs.
Enterprise Governance and Access Control
Security does not stop at encryption. Letro also provides organisation-aware controls for roles, approvals, and policy-driven workflows.
1. Organization-Aware Structure
Model communications around departments, legal entities, teams, and external counterparts. This makes Letro a perfect secure Slack alternative with video and voice call.
2. Role-Based Access Control
Define who can view, send, approve, escalate, or administer communications.
3. Approval and Escalation Workflows
Support templates, review steps, escalation paths, and audit-friendly process design.
4. Governance Without Breaking Security
Keep enterprise controls around the workflow while preserving end-to-end protection for message content.
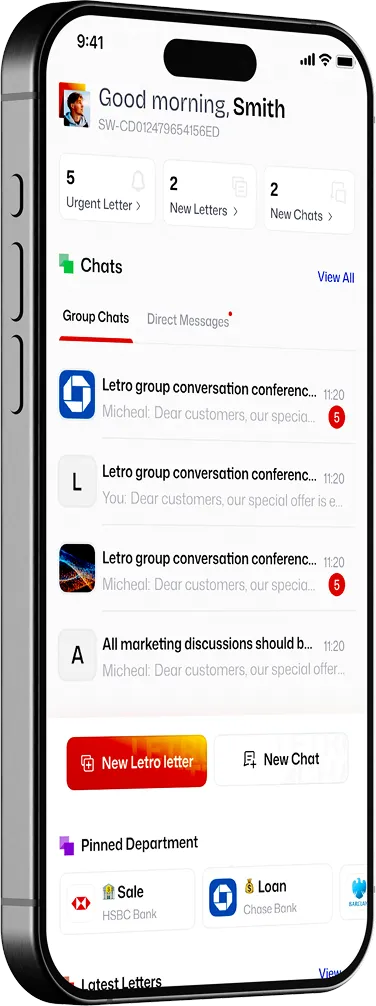
Discuss Your Deployment Model
Whether you need a standard rollout, private infrastructure, or stricter residency and isolation requirements, Letro gives you a trustless foundation for secure client communication.

