Private & Air-Gapped
Deployment
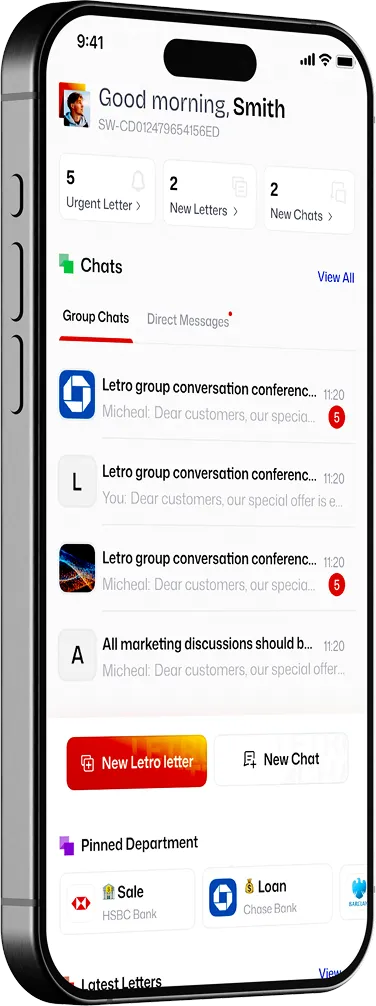
Deploy Letro in the model that matches your risk profile, from faster managed rollout to dedicated and isolated environments with private intranet connection.


One platform, several trust models
Not every organisation needs the same boundary. Some teams want fast onboarding and lower operational overhead. Others need dedicated infrastructure, private cloud, on-premise control, or complete disconnection from the public internet. Strong secure-collaboration vendors already expose those choices directly, rather than forcing every customer into one shared operating model.

Deployment models
Managed deployment
Faster rollout with lower operational overhead.
Dedicated private environment
A separate environment for your users, policies, and administration.
Private cloud or self-hosted deployment
Run Letro in infrastructure you control and align it with your own network and monitoring architecture.
Air-gapped or isolated deployment
For environments where internet connectivity is not permitted or not acceptable as a trust assumption.

How deployment works
Where air-gapped deployment matters

Air-gapped and isolated deployments are used where connectivity itself is part of the risk model — including national security, defence projects, cyber-incident response, industrial control environments, healthcare protection, and parts of financial services. That is why the air-gap story matters commercially: it signals that the platform is designed for higher-assurance environments, not just ordinary SaaS convenience.

Deployment is more than hosting
Discuss deployment
Tell us your operating model, network boundary, and risk requirements. We’ll map the right deployment path.

