Regulatory
Alignment
Built to support regulated communication — without pretending every deployment is automatically compliant.


Alignment, not blanket claims
Letro is aligned with regulatory and support compliance, the actual compliance depends on deployment, configuration, internal policy, access control, retention, incident response, and governance. In sovereign data center or dedicated server, the complete compliance relies on each specific case.

GDPR and International Transfers
GDPR makes cross-border data movement a real architecture question. The EDPB is explicit that transfers of personal data outside the EEA are restricted.
U.S. companies (and other entities subject to U.S. jurisdiction) are generally required to comply with a valid subpoena issued by a court, grand jury, or authorized government body. This includes data stored domestically or overseas (per the CLOUD Act).
Letro supports region-bound rooms, private deployments, and selectively federated collaboration instead of forcing every conversation into one global tenant. Your data is also resides locally where you are without being exposed to CLOUD Act.

DORA and operational resilience
For financial services, DORA entered into application on 17 January 2025 and is designed to strengthen the digital resilience of banks, insurers, investment firms, and other financial entities against ICT disruptions and cyber incidents.

Letro supports DORA-aligned architecture, and it is not a single closed communications silo: it is an open, federated communications fabric, and Synapse can be installed and operated by the organisation itself rather than only consumed as a shared vendor service.
Letro also supports modern identity and governance patterns that matter in resilience planning. MAS is an OAuth 2.0 and OpenID Provider for Matrix, and upstream OIDC providers can be configured. Combined with room-level power controls, that gives the platform a stronger base for enterprise identity alignment, role separation, and controlled administration.
NIS2 and critical sectors

NIS2 creates a common EU cybersecurity framework across 18 critical sectors and raises expectations around cyber risk management, incident reporting, and resilience. For organisations in or around those sectors, communication tooling is no longer outside the security perimeter.

HIPAA and cloud use
SEC / FINRA communications governance
In financial communications, recordkeeping remains a live enforcement issue. In August 2024, the SEC announced more than $390 million in combined settlements in one recordkeeping sweep, and FINRA continues to treat business communications as part of books-and-records obligations. For this audience, secure communication is not enough on its own; governance and retention questions also matter.
eIDAS and digital documents
Where signatures, timestamps, or electronic documents are part of the workflow, eIDAS is the key EU reference point. The Commission’s own summary notes that eIDAS harmonises e-signatures and trust services across Europe and that electronic documents cannot be denied legal effect solely because they are in electronic form.
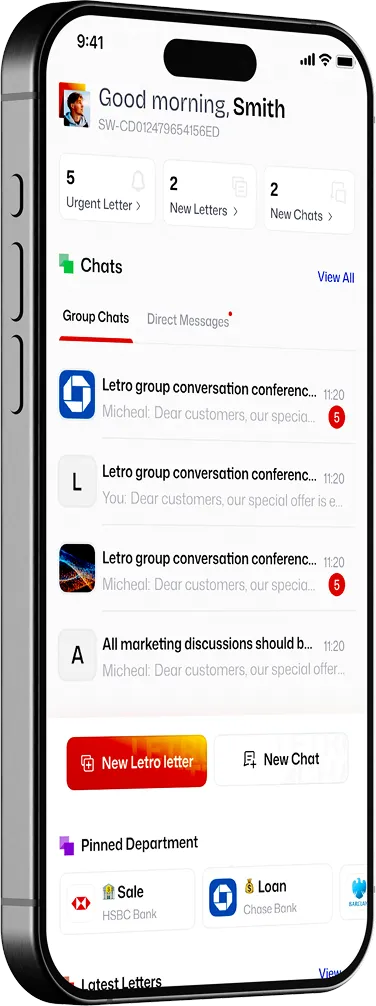
How Letro supports alignment
Letro’s alignment story is built around a few control areas: end-to-end encrypted content, deployment choice, organisational access control, structured workflows, and controlled handling of documents and approvals. The current product story already includes hierarchy, access levels, workflows, signatures, templates, and document handling, and Matrix’s modern auth path supports OIDC-based identity patterns that matter for enterprise governance.
How we talk about regulation
We only describe a framework, certification, or deployment option as supported when it is genuinely available in the deployment being discussed. That keeps the Trust Center useful to security teams and credible to procurement.
Discuss your regulatory requirements
Tell us which frameworks matter to your organisation, and we’ll map the controls, deployment choices, and open questions clearly.

