Security Protocols
& Cryptography
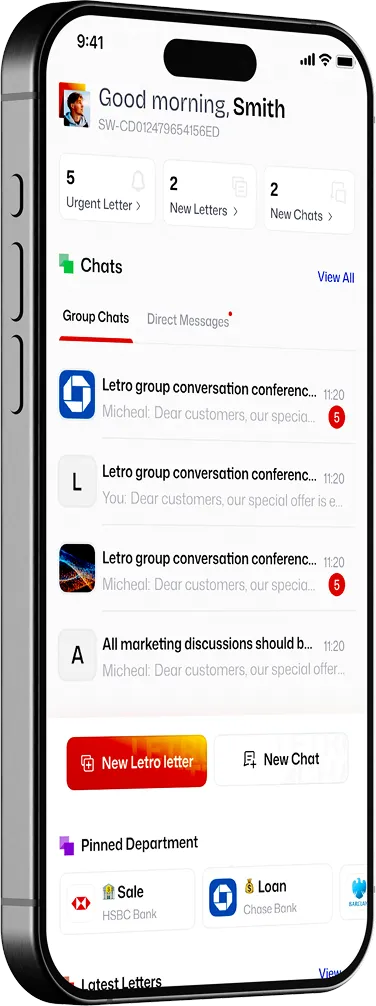
A practical explanation of how Letro protects message content, devices, transport, and federation.


Built on Matrix cryptography
Matrix uses Olm and Megolm for end-to-end encryption. Olm secures peer-to-peer sessions; Megolm secures encrypted group communication. Olm is an implementation of the Double Ratchet protocol popularized by Signal, extended by Megolm for large-scale encrypted group communication.


Letro Protects from A to Z
At the message layer, end-to-end encryption protects content so only authorised devices can decrypt it. Megolm group messages derive an AES-256 key and an HMAC-SHA-256 key. At the transport layer, Letro recommends HTTPS for client-server communication, and federation traffic between homeservers uses HTTPS plus public-key signatures at the TLS and HTTP layers. Device verification adds another layer by helping users confirm the right people and devices are in the conversation.

Interoperable and Auditable
Letro currently exposes some metadata about who is in which rooms to the admins of the homeservers whose users participate in a conversation. That does not defeat end-to-end encryption of content, rather exposing what matters in business context which is critical for auditing.
Letro vs Signal Encryption
Signal’s Double Ratchet is one of the best-known references in secure messaging. Signal’s own specification describes it as a two-party encrypted messaging algorithm where new keys are derived for each message, with protections for earlier and later messages if keys are compromised. Letro’s Olm is in that same ratchet family for pairwise encryption; Letro then adds Megolm for encrypted group messaging in its federated, multi-device model.
Ultra Secure Server with TLS 1.3
TLS 1.3 protects client/server communication against eavesdropping, tampering, and message forgery. TLS is transport encryption, not end-to-end application-layer encryption. HTTPS protects the path; Letro’s end-to-end encryption protects the message content itself.
Publicly Audited by Cyber Firms
Matrix’s cryptography is openly specified, the Rust reference implementation vodozemac has undergone an independent security audit, and recent formal analysis modelled authentication, confidentiality, forward secrecy, and post-compromise security properties for Olm and Megolm.
Request a security briefing
Talk with us about encryption, deployment boundaries, device trust, and the questions your security review team will actually ask.

